The Azure Container Registry is an online repository for storing Docker images (think the Docker Hub).
What’s cool about this is that we can store our images in the same data centre as our deployments, so spinning up containers from the images should be pretty quick. Let’s run through setting up a Registry and pushing an image to it.
But first things first, a quick terminology reminder 🙂
Registry – this is a remote service that will store all our images
Repository – this is a collection of images
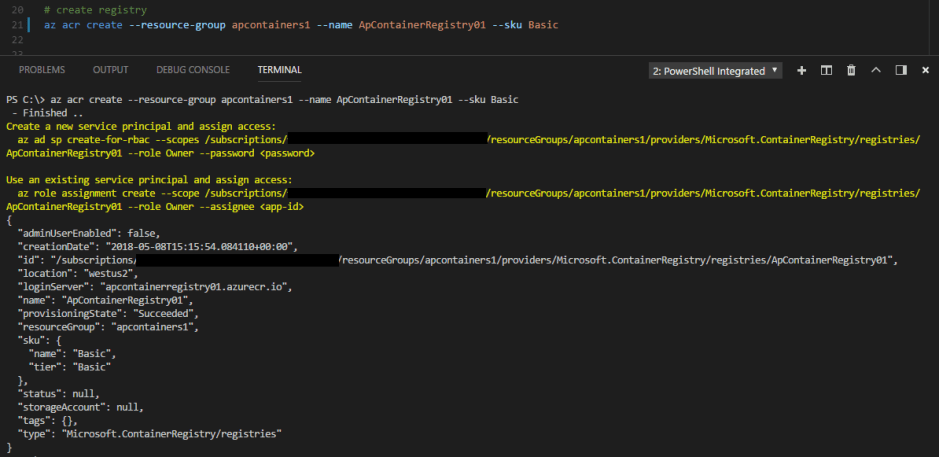
Cool, let’s run through setting up a Registry and pushing an image to it. I’ll be using the Azure-CLI and VS Code with the Azure-CLI plugin. However, I’ll be using a powershell terminal within VS Code. This is because I want to access Docker on my Windows 10 machine, so that I can push an image up to the ACR.
First thing to do is check that the azure-cli is installed: –
az --version
N.B. – You can install it from here if you don’t already have it
Then we need to log in to azure: –
az login
N.B. – You can specify a username and password with this command HOWEVER it doesn’t work for accounts with 2 factor authentication (I mean…really)
Anyway…now we can create a resource group for our registry: –
az group create --name apcontainers1 --location westus2
Then we can create the registry: –
az acr create --resource-group apcontainers1 --name ApContainerRegistry01 --sku Basic
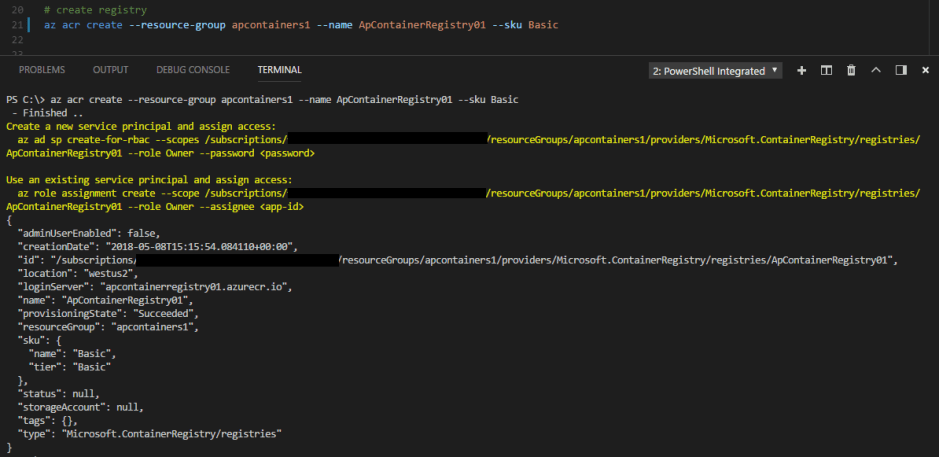
I’m setting this up with the Basic SKU (as this is a demo). You can read more about the Registry SKU levels here
In order to be able to push to the registry, we need to log in: –
az acr login --name ApContainerRegistry01
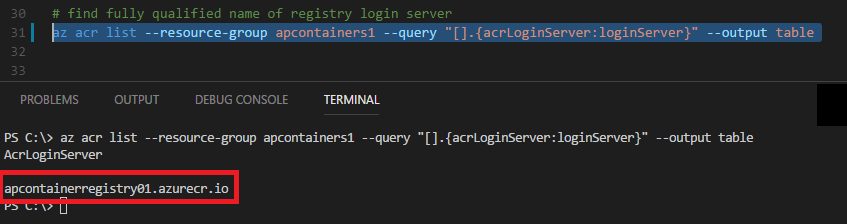
And we also need to get the login server of the registry: –
az acr list --resource-group apcontainers1 --query "[].{acrLoginServer:loginServer}" --output table
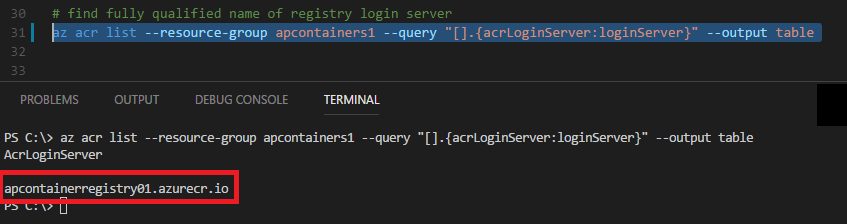
N.B. – save the output of this command.
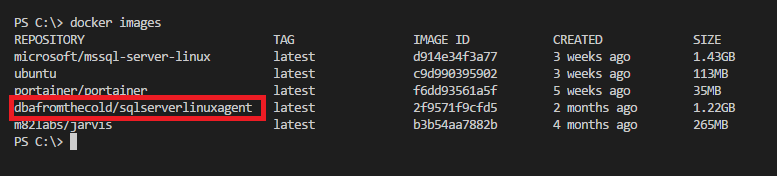
OK, now let’s look locally for an image that we want to push to our ACR: –
docker images
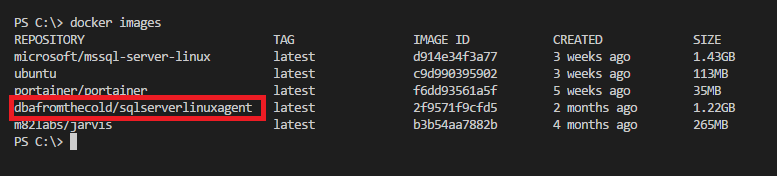
I’m going to push my custom dbafromthecold/sqlserverlinuxagent image. It’s a public image so if you want to use it, just run: –
docker pull dbafromthecold/sqlserverlinuxagent:latest
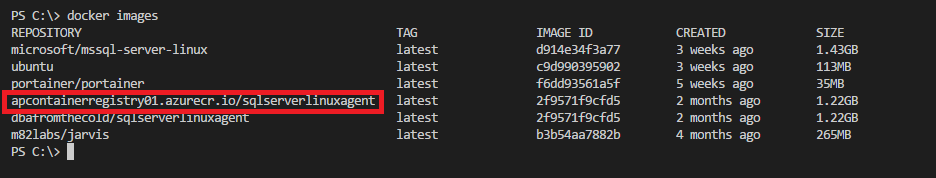
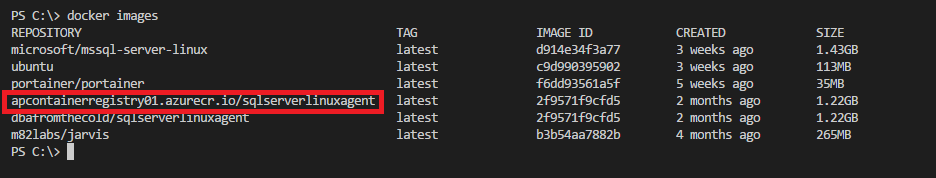
So similar to pushing to the Docker hub, we need to tag the image with the login server name that we retrieved a couple of commands ago and the name of the image: –
docker tag dbafromthecold/sqlserverlinuxagent apcontainerregistry01.azurecr.io/sqlserverlinuxagent:latest
We can see the new tag locally by running: –
docker images
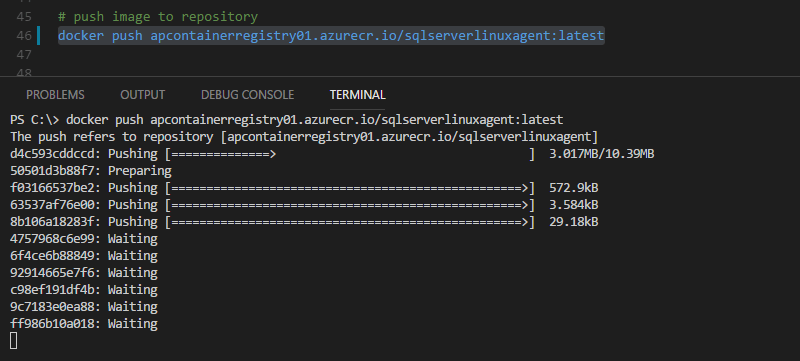
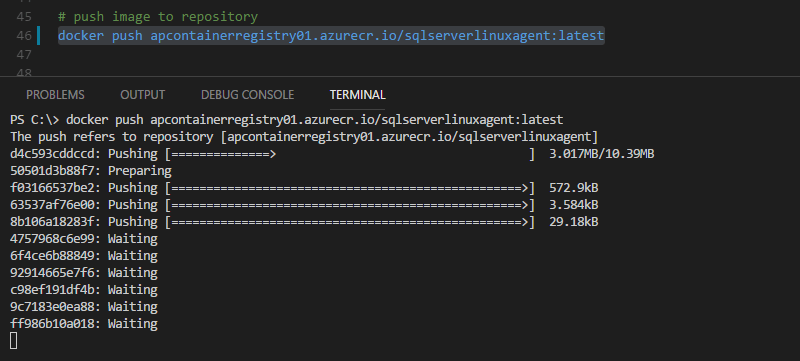
Cool! Ok, so now we can push to the ACR: –
docker push apcontainerregistry01.azurecr.io/sqlserverlinuxagent:latest
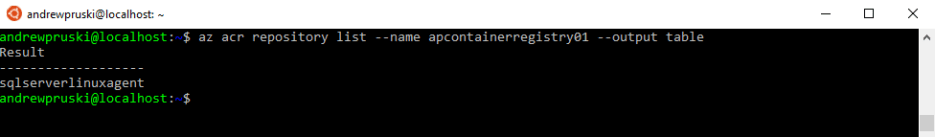
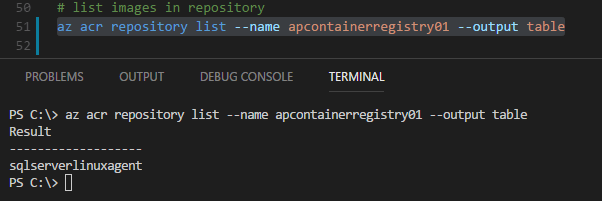
And then confirm that the image is there: –
az acr repository list --name apcontainerregistry01 --output table
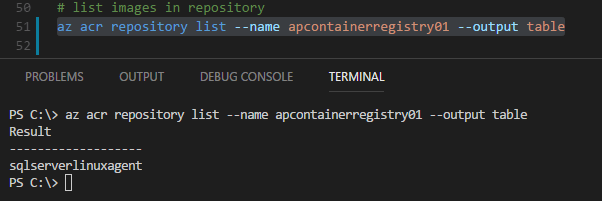
What this has done is create a repository called sqlserverlinuxagent with our image tagged underneath it. To see the image run: –
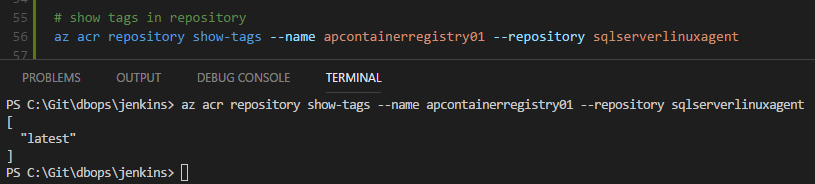
az acr repository show-tags --name apcontainerregistry01 --repository sqlserverlinuxagent
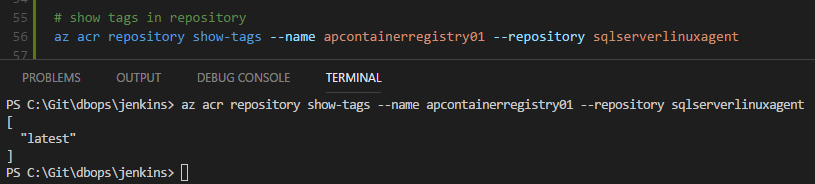
So we have a repository called sqlserverlinuxagent with one image tagged as latest underneath it.
Awesome, now that the image is there we can use it to deploy an Azure Container Instance. I’ll cover how to do that in my next post 🙂
To clean up, we delete the repository: –
az acr repository delete --name ApContainerRegistry01 --repository sqlserverlinuxagent
Oh, if you want to delete the registry…
az acr delete --name apcontainerregistry01
And a more nuclear option (which will delete the resource group): –
az group delete --name apcontainers1
Thanks for reading!