In previous posts I’ve run through how to deploy sql server to Kubernetes using yaml files. That’s a great way to deploy but is there possibly an easier way?
Enter Helm. A package manager for Kubernetes.
Helm packages are called charts and wouldn’t you know it? There’s a chart for SQL Server!
Helm comes in two parts. Helm itself is the client side tool, and tiller, which is the server side component. Details of what each part does can be found here.
So the first thing to do is install Helm. Now you can download the installers from the website here but I found the easiest way to install Helm locally was to install the Kubernetes extension for VS Code. Installing that extension will ask if you want to install other tools, one of which being helm. Nice and easy!
Now install tiller on your cluster (if you don’t have a cluster setup, I have a guide to building one in AKS here): –
helm init
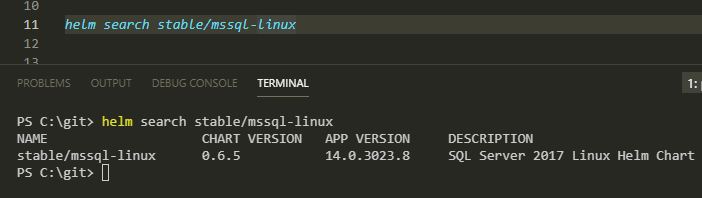
Now search for the mssql-linux package: –
helm search stable/mssql-linux
And deploy!
helm install --name sql-server stable/mssql-linux --set acceptEula.value=Y --set sapassword=Testing1122 --set edition.value=Developer
N.B. – If you get the following error: –
Error: release sql-server failed: namespaces “default” is forbidden:
User “system:serviceaccount:kube-system:default” cannot get namespaces in the namespace “default”
Run the following and then retry the deployment: –
kubectl create clusterrolebinding permissive-binding --clusterrole=cluster-admin --user=admin --user=kubelet --group=system:serviceaccounts;
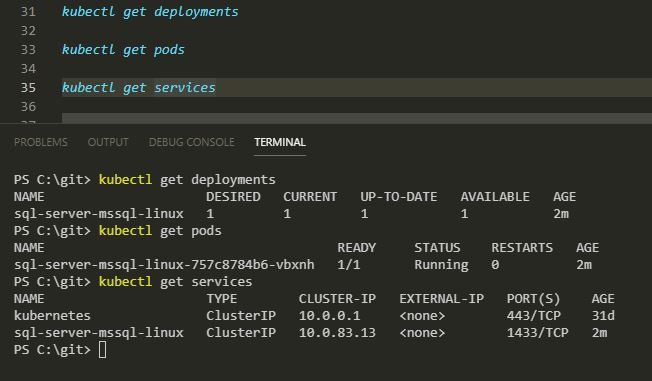
You can check the progress of the deployment by running the following: –
kubectl get deployments kubectl get pods kubectl get services
You may have noticed that the service does not have an external IP. So we can’t connect externally to the SQL instance running in the pod. In order to connect, let’s spin up another pod which has sqlcmd installed and enter a bash session: –
kubectl run sqltools --image=microsoft/mssql-tools -ti --restart=Never --rm=true -- /bin/bash
Now we can connect using sqlcmd: –
sqlcmd -S sql-server-mssql-linux -U sa
And now run a test query: –
SELECT @@VERSION; GO
And that’s how to deploy SQL Server to Kubernetes using Helm! Pretty cool imho.
Finally to delete the deployment: –
helm delete sql-server
Thanks for reading!